Join our newsletter for the inside scoop on Jublia and the events industry


The shift to AI-native event platforms is transforming how events drive connections and audience discovery. But for organizers and enterprise partners, it also raises a critical question: what happens to attendee data when AI begins to process it?
As platforms move from managing data to actively interpreting it, the challenge is no longer just performance — it is trust.
That’s why security must be foundational. AI-native platforms need to be built with a security-first architecture that prioritizes privacy, controlled access, and global compliance from the start.
Modern event platforms manage a wide range of sensitive information. This can include attendee identities and professional profiles, private business meetings arranged through matchmaking, exhibitor lead data collected during exhibitions, and company information shared during networking interactions.
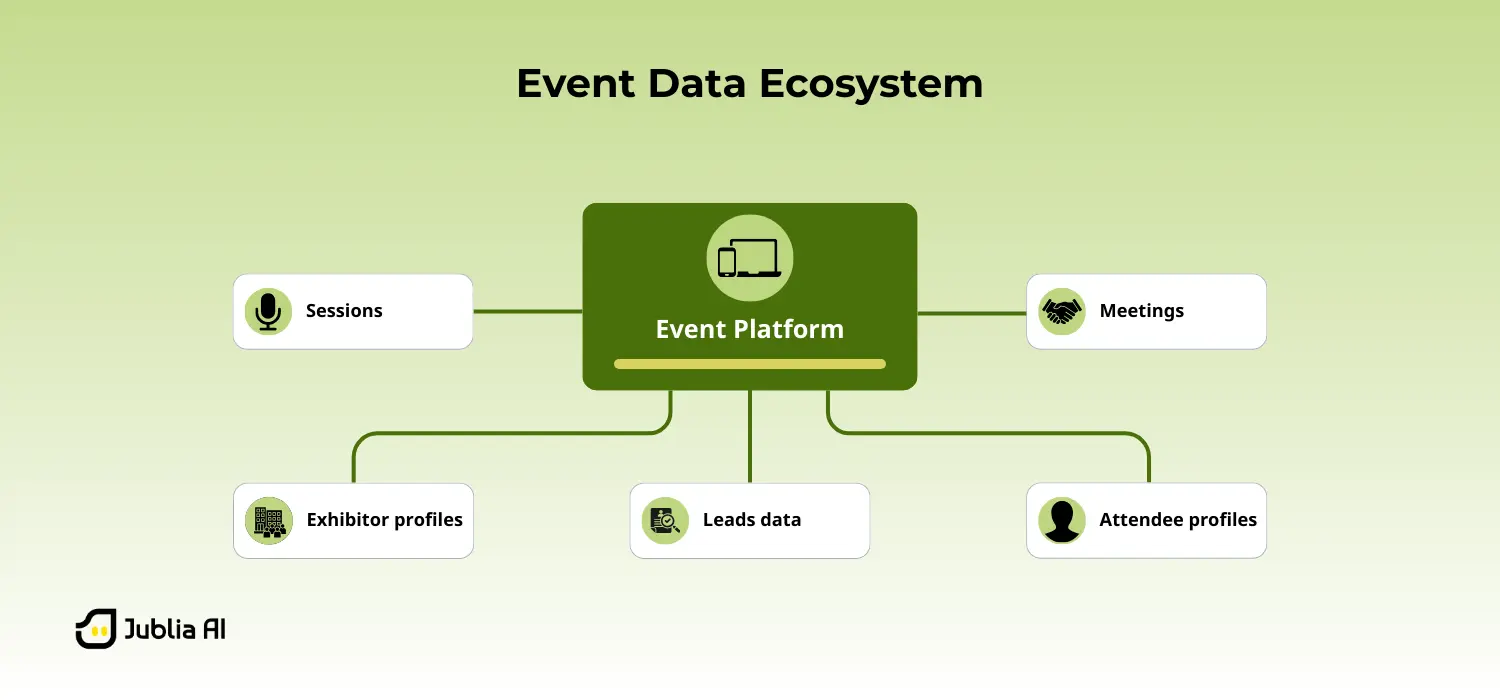
When events operate on AI-native platforms, this data may be processed to generate recommendations and insights that improve discovery and networking. While these capabilities enhance the event experience, they also raise important questions:
For event organizers and enterprise participants alike, security and privacy are essential to ensuring that event technology can be trusted to support meaningful connections and business interactions.
This is why AI-native platforms must embed security directly into their architecture rather than treating it as an additional layer.
Also read: Jublia AI: Why We Evolved and What Stays the Same
Event data moves through several things: from initial setup to live interactions and eventually post-event data management. Each stage requires different security controls to ensure information remains protected.
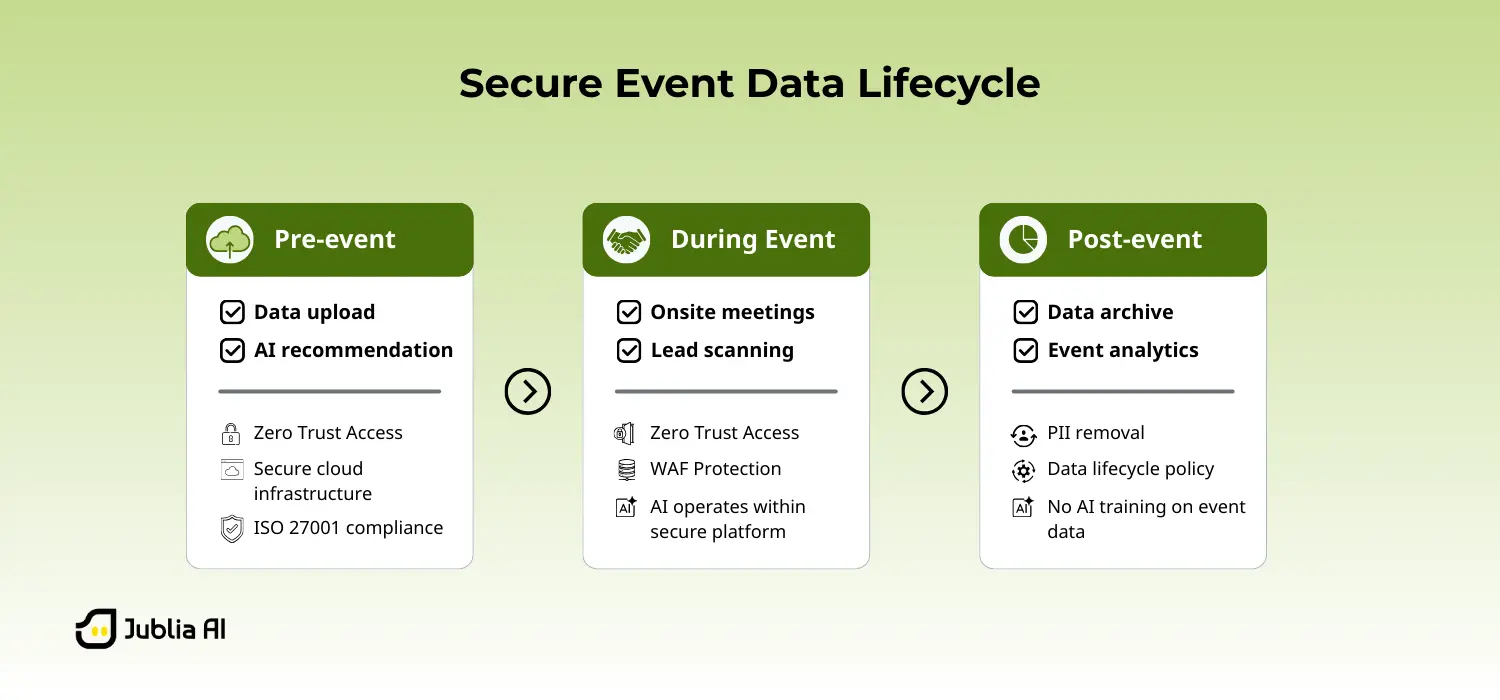
Security begins when organizers upload event information into the platform. This may include attendee lists, company profiles, speaker details, and session agendas.
Jublia AI operates on secure cloud infrastructure hosted on Amazon Web Services (AWS), designed to support enterprise-scale events. Data is protected through industry-standard encryption both in transit and at rest.
We are also ISO 27001 certified, meaning our information security practices meet globally recognized standards for protecting sensitive data.
These foundational controls ensure that event data enters the platform within a secure and controlled environment.
During the event, the platform handles thousands of real-time interactions — from meeting scheduling to lead capture and session discovery.
To secure this activity, Jublia applies a Zero Trust model, verifying every access request and limiting data visibility through role-based permissions. The platform is further protected by a layered approach, including Cloudflare CDN, WAF, and DDoS protection.
Within this environment, Jublia AI processes event data to generate results that improve discovery and networking experiences. However, this data is not used to train AI models, and raw event data is not exposed externally.
This distinction is critical. Many AI systems rely on user data to improve their models, which can create uncertainty around how sensitive information is reused. At Jublia AI, event data remains strictly within the context of the event and is not repurposed beyond its intended use.
This ensures that attendee interactions, business meetings, and event activity remain private and controlled at all times.
Also read: Judy: The AI CX Agent Elevating Customer Experience at Jublia AI
Security responsibilities do not end when the event concludes.
We follow strict data lifecycle management practices, removing personally identifiable information (PII) by the end of the quarter in which the project ends.
Beyond data retention, the platform is designed around strict data isolation. Each event operates within its own data environment, meaning information is never shared, reused, or made accessible across events.
This distinction matters. Event data — including attendee profiles, meetings, and leads — can be highly valuable. In some cases, such data may be reused or aggregated beyond a single event. At Jublia AI, this is not a possibility by design.
This ensures that sensitive data is not stored indefinitely and is not used for AI model training.
As a result, organizers retain full ownership of their data, with the assurance that it remains private and exclusive to their event from start to finish.
Security is an ongoing process rather than a one-time setup.
We continuously strengthen our security posture through vulnerability assessments, penetration testing, and structured patch management processes designed to identify and resolve potential weaknesses.
Advanced monitoring systems also help detect suspicious activity early, allowing threats to be mitigated before they impact the event experience.
Many events involve participants from multiple countries, each governed by different privacy regulations.
To support global event ecosystems, we align our security practices with international privacy frameworks including the General Data Protection Regulation (GDPR) in Europe and the Personal Data Protection Act (PDPA) in Singapore.
Privacy-by-design principles guide how event data is collected, processed, and protected within the platform.
As events become increasingly AI-native, security becomes even more critical to the success of the event ecosystem.
Attendees must trust that their information is protected. Exhibitors must trust that their leads remain secure. Organizers must trust that their event data stays under control.
By embedding security directly into platform architecture — from infrastructure and access control to privacy and data lifecycle management — AI-native systems can deliver intelligent event experiences without compromising trust.
Because in modern events, intelligence and security must evolve together. Discover how Jublia enables secure, AI-native event experiences — book a demo to see it in action.
 Securing AI-Native Events: How Event Data is Protected from Start to Finish
Securing AI-Native Events: How Event Data is Protected from Start to FinishA detailed explanation on how Jublia AI handles data security
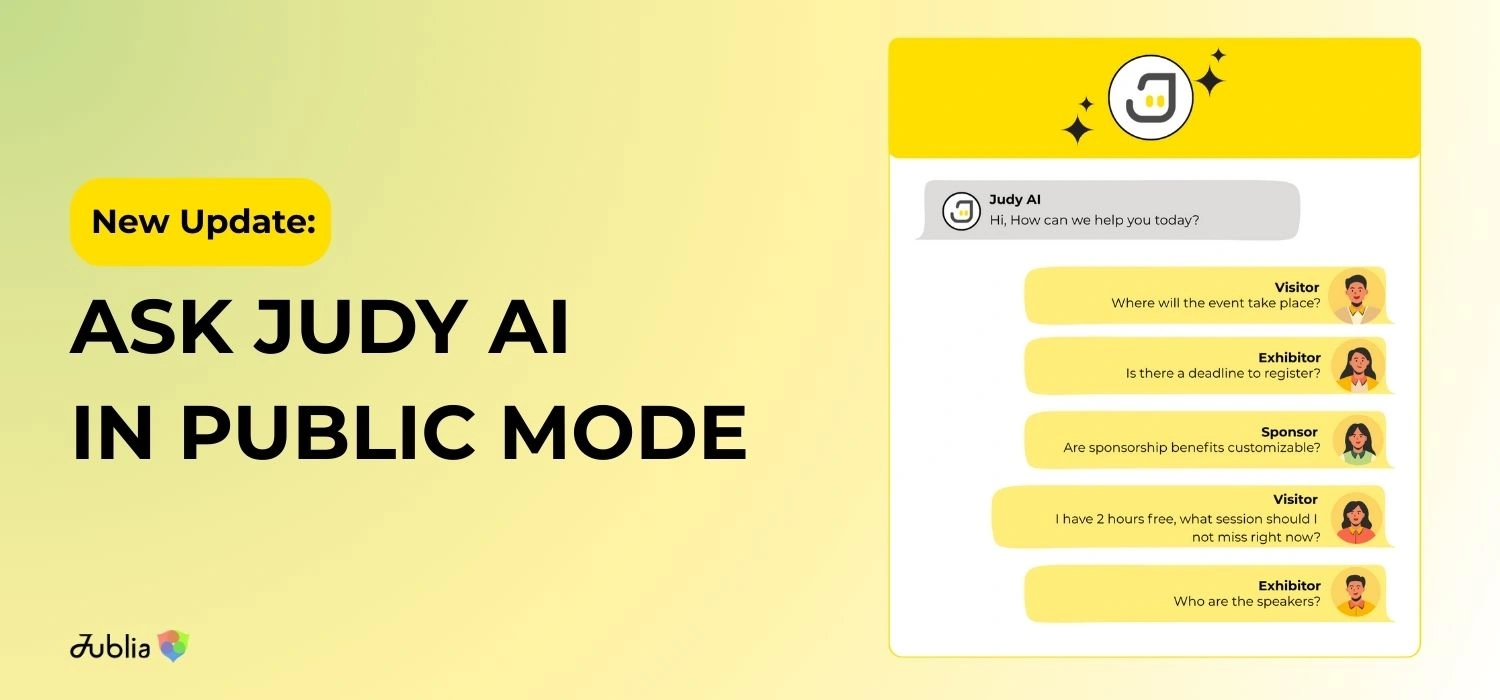 Ask Judy AI in Public Mode: AI Chatbot for Your Event Website & Platform
Ask Judy AI in Public Mode: AI Chatbot for Your Event Website & PlatformCapture conversations, drive conversions, and spark interest for public audience
 Judy: The AI CX Agent Elevating Customer Experience at Jublia AI
Judy: The AI CX Agent Elevating Customer Experience at Jublia AIAn AI-Native approach to customer support


